What is Cloud Security and Why is it Necessary?
Mar 31, 2026

Cloud computing security is a hot topic as more businesses are increasingly moving away from traditional, on-premise software and infrastructure to the cloud. Spending on cloud system infrastructure services is expected to grow to about $947.3 billion in 2026.
|
“Don’t assume that all of the cybersecurity measures you used on premises will inherently apply to cloud computing.” – Danny Tehrani, Owner, Computers Made Easy |
That being said, there are new network security risks and challenges to consider when it comes to securing your sensitive information in the cloud. After all, 45% of all data breaches now occur on cloud systems.
In this blog post, we’ll explore what cloud computing security is, the different types, and some of the key considerations for keeping your data safe in the case that an attack surfaces.
What Is Cloud Computing Security?
Cloud computing security is an umbrella term that covers a wide variety of cloud security solutions used to protect your services and data in cloud-based infrastructure.
Its primary purpose is to control data access within your cloud environment and ensure only authenticated users can access sensitive data. Protection also includes controlling how data is stored, preventing malicious activity from entering the system, maintaining the confidentiality and integrity of files, and ensuring you remain compliant with regulatory laws.
Achieving cloud security requires identifying tangible threats that can impact your systems and developing effective strategies for mitigating them with cloud services.
The first step in achieving this goal is to gain a thorough understanding of cloud security. Continue reading to gain insight into the following questions:
-
What is data security in cloud computing?
-
What is infrastructure security in cloud computing?
-
What is cloud security threats analysis?
-
What is cloud workload security?
80% of Companies Suffer a Cloud Attack Every Year
Find out what the other 20% do to keep their data safe
Cloud Security Components Overview
Cloud security covers a wide range of components, such as cryptographic services, access controls, auto-patching, advanced user authentication processes, and compliance functions. Each one helps ensure your data remains safe from malicious threats throughout the various life cycles of the system itself.
Let’s break it down.
What is Data Security in Cloud Computing?
Data security in cloud computing refers to protecting structured and unstructured data stored in the cloud from unauthorized access, use, and manipulation by external sources.
Data security measures usually include:
-
Encryption techniques
-
Employee training programs
-
Access control protocols
Along with many other safeguards to prevent malicious attacks or theft of sensitive information, these steps are critical in safeguarding customer data or corporate records.
What is Infrastructure Security in Cloud Computing?
Infrastructure security in cloud computing is an essential part of keeping cloud-based data safe. It involves using secure networks, firewalls, and other technologies to protect against unauthorized access, cyber attacks, and data loss.
It includes:
|
Access control |
Controls who can access systems and data by verifying identities and assigning the correct permissions. This limits unauthorized use. |
|
Application security |
Focuses on securing applications from vulnerabilities through updates, secure coding, and testing. This reduces the risk of attacks targeting apps. |
|
Firewalls |
Monitors and controls incoming and outgoing network traffic based on rules. This blocks unauthorized access and suspicious activity. |
|
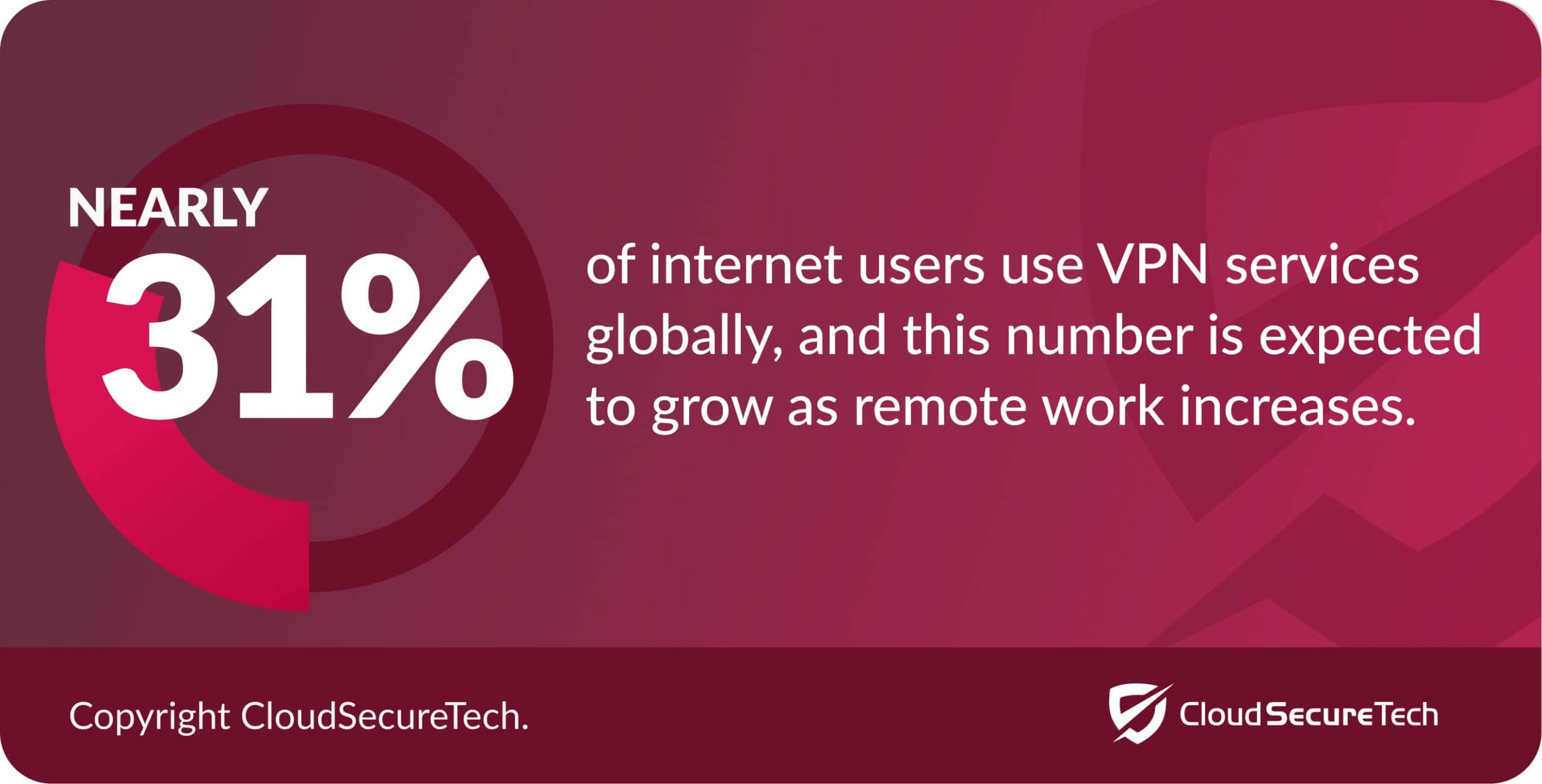
Virtual private networks (VPN) |
Creates an encrypted connection between a user and the network. This protects data when users access systems from outside locations. |
|
Behavioral analytics |
Analyzes user and system behavior to detect unusual actions. This helps identify potential threats early. |
|
Intrusion prevention systems |
Detects and stops malicious activity within a network. This prevents attacks before they cause damage. |
|
Wireless security |
Secures Wi-Fi networks through encryption and access controls. This prevents unauthorized devices from connecting and accessing data. |
Infrastructure security also includes making sure those who have access only do so with the correct authorization. To do so, a monitoring system should be implemented to track activity and alert administrators if suspicious activity is detected.
Implementing strong infrastructure security measures for cloud computing can be a worthwhile investment for businesses looking to safely store important information online. If you’re one of the 16% of American businesses that operate on a fully remote work model, it’s also valuable to add a VPN to your infrastructure to ensure safe browsing from anywhere.
 Source: CloudSecureTech
Source: CloudSecureTech
What is Cloud Security Threat Analysis?
Cloud security threats analysis is a type of cloud security that helps identify and assess risks that could potentially put your organization’s applications, data, or services at risk of exploitation.
The analysis involves analyzing external sources to see if there are any potential vulnerabilities in the environment, as well as looking for evidence of suspicious activity from within the network.
Once these threats are identified, appropriate security measures can be implemented to reduce the risk of exploitation.
Components of security threats analysis include:
-
Threat modeling
-
Cloud security posture management (CSPM)
-
Automated patch management
-
Identity and access management (IAM)
What is Cloud Workload Security?
Cloud workload security enables users to safeguard applications, services, and capabilities on virtual machines, databases, and even containers from potential threats or cyber attacks.
Here are some key aspects of cloud workload security:
-
Vulnerability management
-
Container security
-
Cloud workload protection platform (CWPP)
82% of organizations use hybrid cloud environments for their enterprise application workloads, meaning they use a combination of on-premise, private cloud, and public cloud deployments to choose the appropriate environment depending on the workload.
Are you curious to learn more about cloud security and how to protect your network from vulnerabilities? Check out these additional resources.
Additional Resources About Cloud Computing Security
Implement Cloud Security Into Your Business
When it comes to securing your cloud platforms, you’ll want to rely on a managed service provider (MSP) to help you navigate through cloud security challenges.
Whether you need help with a successful cloud migration or enhancing your existing cloud infrastructure security measures, Computers Made Easy can assist with:
-
Encryption
-
Firewalls
-
Cloud security updates
-
Establishing security controls
-
Access management
-
Managing cloud data and applications
-
Private cloud configuration
-
Team training on security responsibilities
-
Encryption keys implementation
Book your free consultation today to learn more about how we can help you complete your digital transformation!




